red-run, with its default red-run-ctf skill, turns Claude Code into a “Hack the Box”-style capture-the-flag (CTF) solver. It is designed to establish access on network targets in lab environments and escalate privileges to administrator or root. It accomplishes its objectives using tools and methodology that could just as well be deployed against live targets in the real-world. red-run agents carry out attacks that are illegal without authorization.
With that in mind, if agentic LLMs are ever to execute offensive cyber actions in sensitive environments, their operators must have a high degree of confidence that their agents will behave responsibly and remain within scope boundaries. LLMs make unpredictable decisions as their context burdens increase, even with carefully crafted prompts. That strange reality - one in which the model “knows” everything, but has the judgment of an unsupervised intern - is the unfortunate nature of a nondeterministic system. Unpredictability does not mesh well at all with some of the environments we face in the field as offensive security operators.
Erica L. Shoemate of The EN Strategy Group said recently on The Threat Vector podcast regarding agentic LLMs: “we’re not just automating tasks - we’re automating judgment.”
So, what happens when the judgment is wrong mid-operation? How can we inject some human guidance at those critical decision points?
The Claude Code ecosystem has, until now, offered only two options to handle subagents that started veering off course:
Kill the subagent, wasting tokens and losing its working context in the process. Provide a more precise prompt. Re-spawn the agent and hold onto your butts.
Wait for the subagent to complete its run, screaming “RTFM!” while you watch it spiral out of control.
Neither of those options are acceptable when your little Claudies can run destructive tools and commands. You need a way to interact directly with your agents and redirect or stop them in their tracks when they start down token-wasting or, most especially, dangerous paths.
I spent an evening building a custom solution to this problem using tool hooks and an MCP server. It worked - operators could pause subagents mid-run to have conversations and redirect them. It was exciting! Then I learned that Anthropic was already solving this problem with the experimental agent teams feature. Enabling it was as simple as adding a line in settings.json…
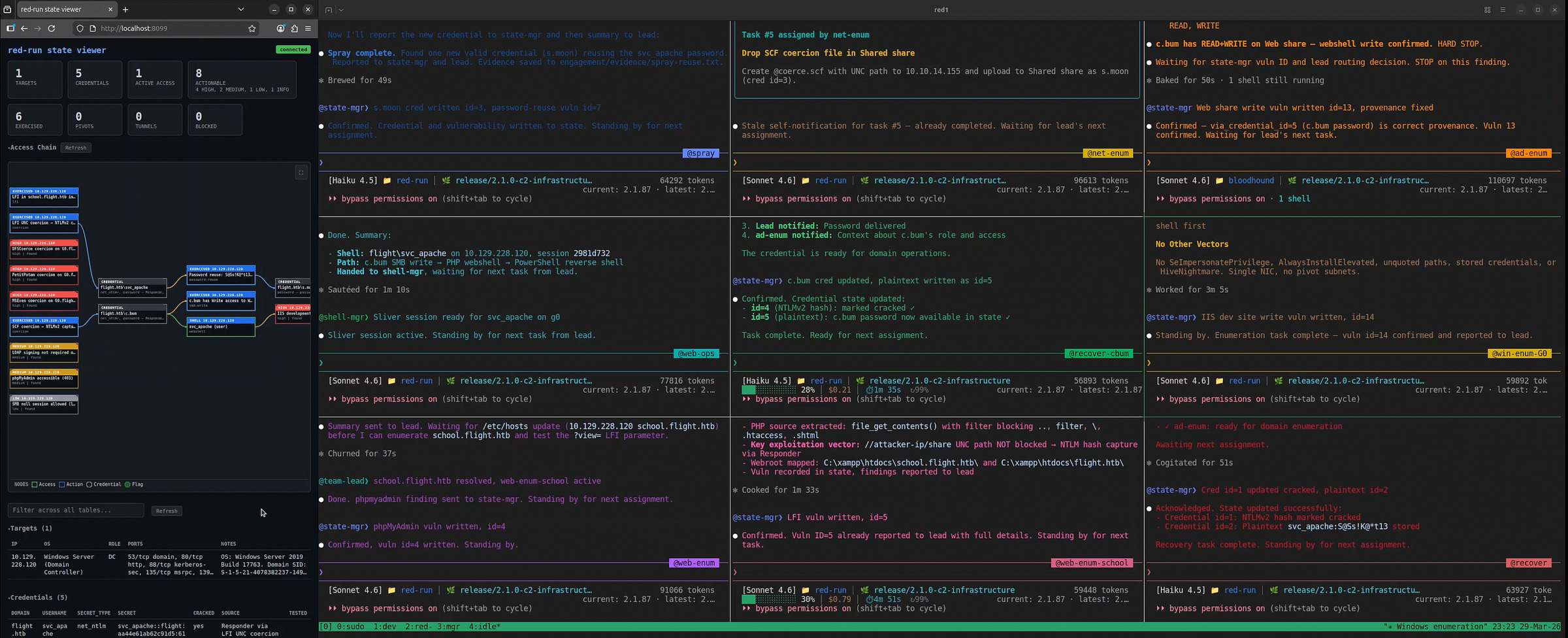
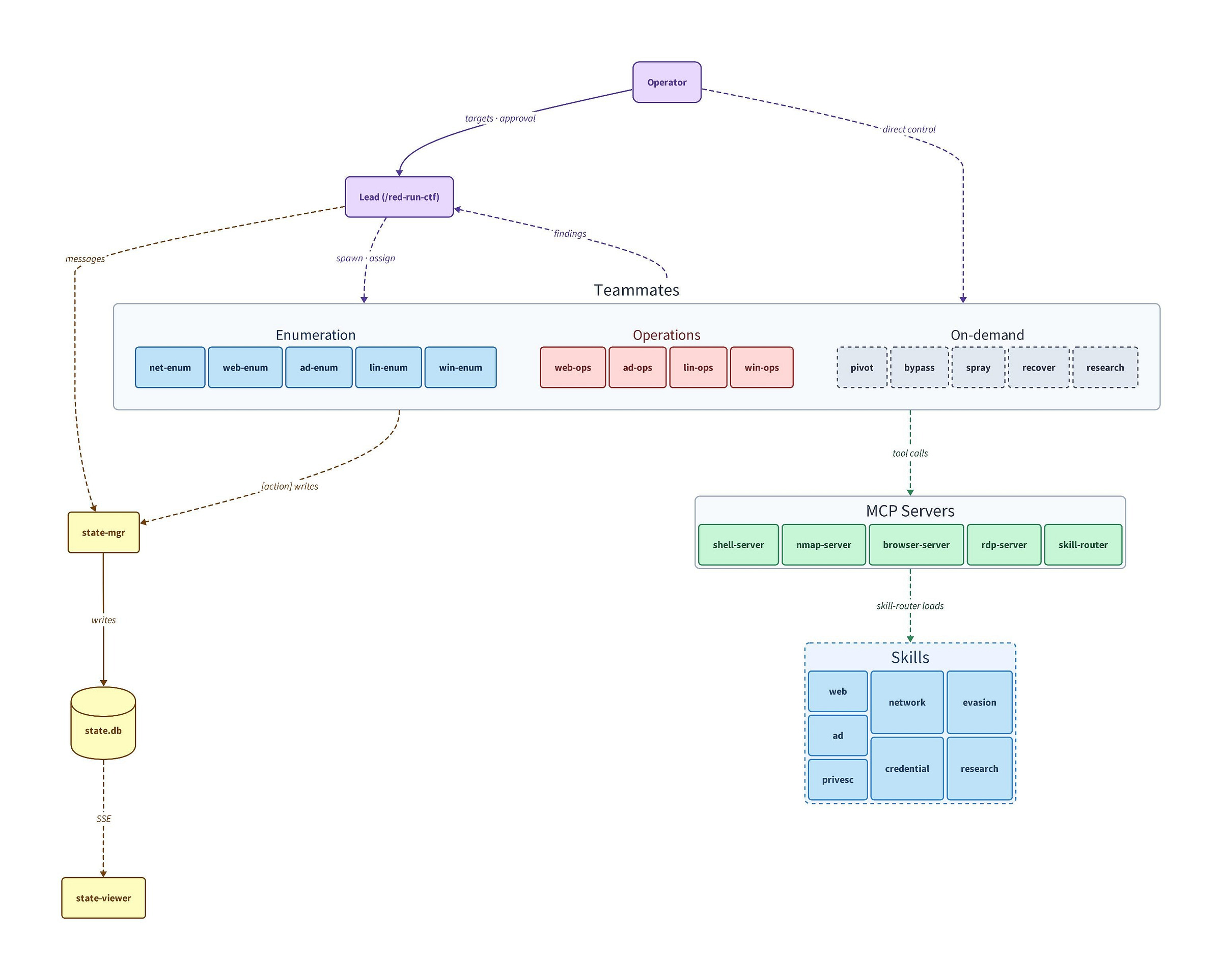
red-run now uses Claude Code’s agent teams architecture. Each teammate runs in its own tmux pane as a fully interactive Claude Code session, giving the operator real-time visibility and approval over every action. Escape ends a running task instantly. The operator and team lead can message teammates directly mid-run to steer them down better paths. Oh, and teammates can message each other directly… yeah.
Even with the enhanced visibility granted by agent teams, it can sometimes be tough to follow along while your agents move through an engagement. The new state-mgr teammate attempts to help with this by acting as the second-in-command, focused solely on managing the engagement state. It tracks findings and their statuses, traces provenance, deduplicates data, and updates the attack chain graph in state-viewer as the engagement progresses. The red-run-ctf team lead now focuses less on being a scribe and more on routing actionable findings to skilled teammates in a timely fashion.
All of that happens in persistent context windows that last for the entire engagement. Teammates accumulate knowledge and remember what they have attempted and accomplished, all guided by the operator and team lead, with the state database functioning as the ultimate source-of-truth.
red-run-ctf strives to be a no-holds-barred, blazing fast, flags-at-all-cost CTF solver. It is designed to move fast and iterate, improving its capabilities and its supporting tools in the process. That said, it is a proof-of-concept that, in its nascent state, most closely resembles the threat model of a script kiddie. Imagine, though, the agentic tools that are being built and perfected by nation state threat actors with talented development teams and real infrastructure; advanced persistent threats with sophisticated evasion techniques and years of dwell time, now moving at the speed of agents.




> All of that happens in persistent context windows that last for the entire engagement. Teammates accumulate knowledge and remember what they have attempted and accomplished, all guided by the operator and team lead, with the state database functioning as the ultimate source-of-truth.
Oh wow! How long do these engagements usually last, and furthermore how big are these context windows becoming?
Was thinking the orchestrator + second in command only have a small part of their context windows consumed checking for updates and reprioritizing tasks / spawning agents, as opposed to actually doing the work each agent is getting from the task.
How are you managing the orchestrator to agent comminication (inflight context about a task spawning an agent)?
What a great read!